Chapter 10 Performance Monitors Extension
10.1 Support and discovery
Performance monitoring facilities are optional. When implemented, the SMMU has one or more Performance Monitor Counter Groups (PMCG) associated with it. The discovery and enumeration of a base address for each group is IMPLEMENTATION DEFINED. The Performance Monitor Counter Groups are standalone monitoring facilities and, as such, can be implemented in separate components that are all associated with (but not necessarily part of) an SMMU.
Note: A centralized ID scheme to identify common properties is not currently exploited because PMCGs might be independently-designed, and contain their own identification facilities.
10.2 Overview of counters and groups
The SMMU performance monitoring facility provides:
-
A number of specified events can be detected that correspond to behavior of aspects of the SMMU or the implementation.
-
A number of counters that increment when their configured event occurs.
An implementation has one or more counter groups, and each group contains 1 - 64 counters. Each group has a discoverable set of supported events which can be counted by the counters within the group. All counters in a group can be configured to count any of the supported events. Different groups are not required to support the same set of events.
For example, a particular distributed SMMU implementation might have two groups:
-
A group for a unit performing translation table walks and counting translation-related events
-
A group for a separate unit containing TLBs and counting TLB-related events.
Some event types are not attributable to one traffic StreamID and are considered to be common to all. Other events are generated by a specific stream and can be filtered by StreamID so that a counter increment is enabled when the StreamID filter matches the event’s originating StreamID.
Counters associated with a group are not required to be able to count events that originate from all possible StreamIDs. A counter group is permitted to be affiliated with a subset of incoming StreamIDs. Arm strongly recommends that the incoming StreamID namespace is covered by the union of all counter groups, so that events from any StreamID can be counted using a counter in a group appropriate to the StreamID value. The discovery of whether a given group counts events from a given StreamID, that is the mapping of a StreamID to supporting group or groups, is IMPLEMENTATION DEFINED.
Multiple counter groups might count events that originate from the same StreamID or StreamIDs, or from overlapping sets of StreamIDs.
Note: Because counter groups are not required to support the same kinds of events, events that originate from a given StreamID might be counted in several groups, if multiple groups are associated with that StreamID.
Note: Taking the previous example of the distributed implementation, activity from a given StreamID might cause TLB miss events that can be counted in the group associated with a TLB unit, whereas the same StreamID might cause translation table fetch events that can only be counted in the other counter group associated with the translation table walk unit.
0 StreamID namespace N
Group 0 Events A, B, C
Group 1 Events D, E
Group 2 Events D, E
Group 3 Events D, E
Group 4 Events D, E
Figure 10.1: Example counter groups filtered on events from different StreamID spans
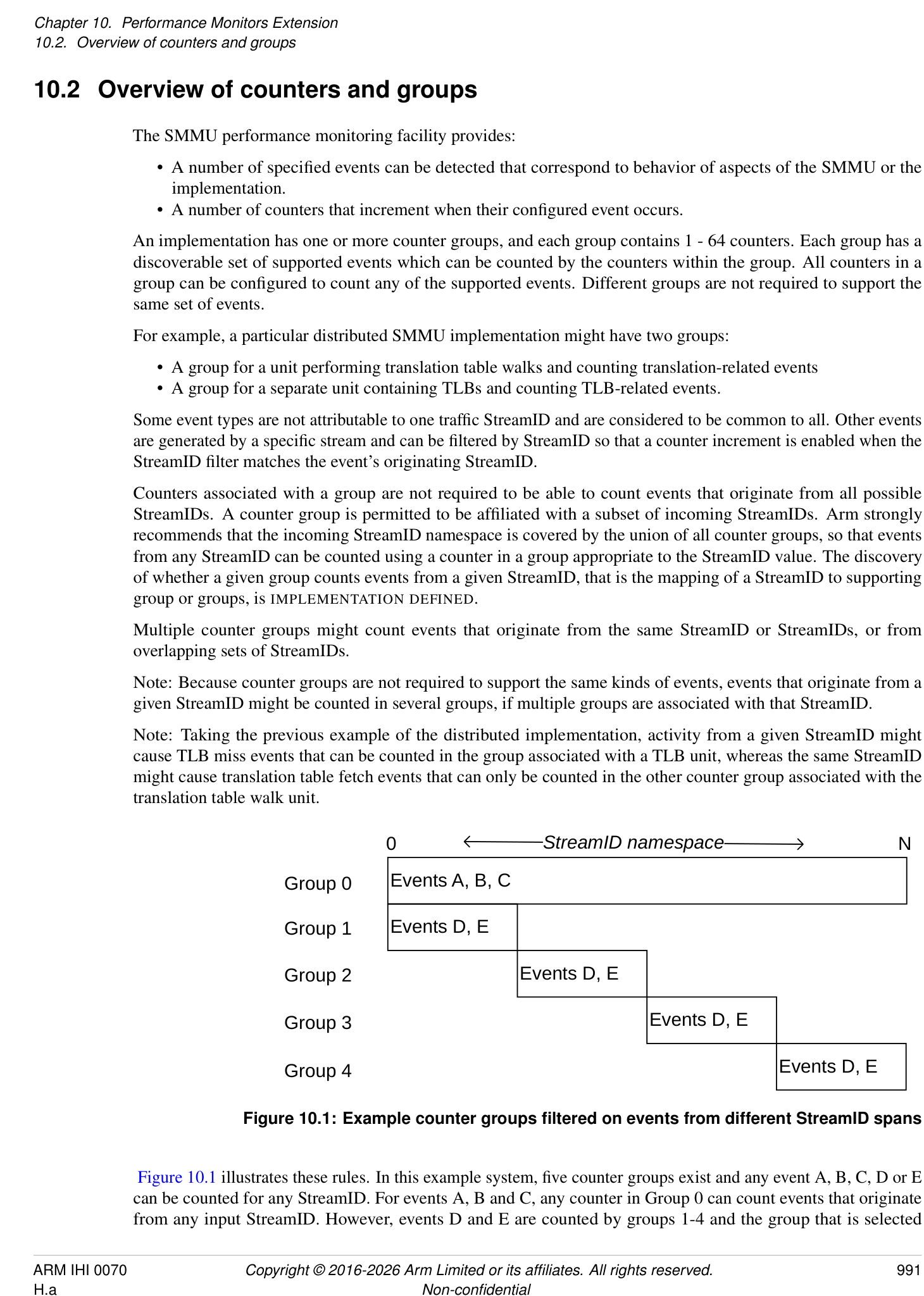
Figure 10.1 illustrates these rules. In this example system, five counter groups exist and any event A, B, C, D or E can be counted for any StreamID. For events A, B and C, any counter in Group 0 can count events that originate from any input StreamID. However, events D and E are counted by groups 1-4 and the group that is selected
depends on which services the relevant StreamIDs. For example, to count event D originating from StreamID N, a counter in Group 4 must be used.
Note: Although a counter can be configured to count an event that is filtered by StreamID N, a counter can also be configured to count an event without the StreamID filter. In the example in Figure 10.1, a counter in Group 4 could count an event that occurs from any of the StreamIDs associated with Group 4.
If a counter group exists that is associated with all StreamIDs, Arm recommends that Group 0 is used.
The association between counter groups and ranges of StreamIDs is fixed at design time and no mechanism is provided to re-configure this mapping.
A counter group is conceptually free-standing and has no interdependency on the behavior of other counter groups or even on the SMMU configuration itself. This means that:
-
A counter group can be dissimilar to other groups, for example if implemented in a different IP block to another group.
-
The capabilities of a given counter group (events captured, number of counters, MSI support) might be unique in the SMMU.
If the SMMUEN for a Security state is zero, it is IMPLEMENTATION DEFINED whether events that can be filtered by stream are counted for activity on the streams that are associated with that Security state. The Secure Observation rules in 10.6 Support for Secure state also apply if the implementation supports counting the event in this scenario.
For events that cannot be filtered by stream, it is IMPLEMENTATION DEFINED whether they are counted when all traffic through the SMMU is treated as global bypass, as indicated by SMMU_(*_)CR0.SMMUEN == 0.
Note: Event 0, “Clock cycle” is the only architectural event in this category.
Unless otherwise specified, when the configuration is changed, there is an IMPLEMENTATION SPECIFIC delay between the observation of the register write by the PMCG and the configuration change taking effect. The change is not required to affect transactions that have been observed and might be partly processed by the SMMU.
Note: Arm expects that any delay is small. Register accesses and client transactions that occur after the completion of a register access that alters the configuration are expected to observe the new configuration.
10.2.1 Overflow, interrupts and capture
An individual counter overflows when an increment causes a carry-out to be generated, that is when the counter wraps beyond its maximum unsigned value to a smaller value. When this happens, a bit is set in the Overflow Status array that corresponds to the counter that overflowed. An overflow condition does not prevent a counter from counting.
Note: Software can read the Overflow Status (OVS) array using the SMMU_PMCG_OVS{SET0,CLR0} registers to determine which counters have overflowed.
A counter can be programmed to assert a common per-counter group interrupt, when enabled, on overflow. In addition, the counter group interrupt has a per-group overall enable flag.
Note: Whether an overflow occurs is independent of, and not prevented by, the OVS status. If a counter overflow occurs, any side effects of interrupting and capturing it, if enabled, occur regardless of the value of the corresponding OVS bit.
The counter group interrupt is an edge-triggered wired interrupt output, an MSI interrupt, or both. Because counter groups might represent distinct IP blocks, MSI support can differ between counter groups that are associated with one SMMU. However, Arm strongly recommends that all counter groups support MSIs if the core SMMU supports MSIs.
Note: As with the core SMMU MSI IRQs, an implementation that supports MSIs can still supply a wired IRQ output, giving the system the choice of using the wired IRQ and leaving the MSI disabled, or using the MSI.
Optionally, a PMCG can allow all counter registers in a group to be simultaneously sampled by a capture mechanism that copies the counter values to their respective shadow register. The presence of support for this mechanism
is discovered via SMMU_PMCG_CFGR.CAPTURE == 1. The capture mechanism is triggered by one of the following:
-
A write of 1 to SMMU_PMCG_CAPR.CAPTURE.
-
Overflow of a counter configured with SMMU_PMCG_EVTYPERn.OVFCAP == 1.
- Note: The counter that causes the capture due to overflow is captured with a post-overflow value.
-
An external IMPLEMENTATION DEFINED mechanism.
When capture is triggered by a write to SMMU_PMCG_CAPR.CAPTURE, the captured values are observable to an access that is performed after the write to SMMU_PMCG_CAPR completes.
Note: One use model for the PMCG might be to program a counter to overflow within a known number of counts and, on overflow a capture is triggered and an interrupt is sent. The interrupt handler reads out the captured counter values.
Note: In addition, counter values and their overflow events can be exported in an IMPLEMENTATION DEFINED manner to external profiling logic. Export and capture of counter values through a mechanism that is invisible to the SMMU PMCG programming interface are unrelated to the presence of the programmatic capture mechanism indicated by SMMU_PMCG_CFGR.CAPTURE.
If an MSI is configured with a cacheable, shareable attribute, whether the PMCG is able to perform a cache-coherent MSI write is IMPLEMENTATION DEFINED. The core SMMU_IDR0.COHACC field does not apply to PMCG MSI writes.
When a counter that overflows is configured to trigger an interrupt, the interrupt is made observable after all of the following have become observable:
-
The update to OVS.
-
The new counter value.
-
The captured values, if the overflow that caused the interrupt also triggered a capture.
10.3 Monitor events
Performance events are indicated by a numeric ID, in the following ranges:
-
0x0000 to 0x007F: Architected events
-
0x0080 to 0xFFFF: IMPLEMENTATION DEFINED events
The architecture defines the following event types and their causes. Unless otherwise specified, “translation request” includes both ATS Translation Requests and non-ATS translation requests.
| Event ID | Description | Notes | Mandatory | Can flter on StreamID |
|---|---|---|---|---|
| 0 | Clock cycle | The period between these events is | Y | N |
| IMPLEMENTATION DEFINED. | ||||
| It is IMPLEMENTATION DEFINEDwhether this | ||||
| event is derived from a continuous time base or | ||||
| an SMMU clock which might be subject to | ||||
| IMPLEMENTATION SPECIFICgating based on | ||||
| SMMU activity. | ||||
| 1 | Translation or | For a component processing client device | Y | Y |
| request | transactions, this event counts once for each | |||
| transaction. | ||||
| For a component performing translation | ||||
| services, this event counts once for each | ||||
| translation request received from another | ||||
| component. | ||||
| This event includes transactions or translation | ||||
| requests that lead to TLB or cache misses. This | ||||
| event may include any or all of the following: | ||||
| - Terminated transactions. | ||||
| - Prefetch transactions. | ||||
| - CMOs. | ||||
| - ATOS requests. | ||||
| - HACDBS processing. | ||||
| See footnotes (1), (2), (3). | ||||
| 2 | TLB miss caused | This event is counted once when translation for | Y | Y |
| by incoming | an incoming transaction or translation request | |||
| transaction or | cannot be satisfed from internal TLB caching, | |||
| translation request | and depends on a translation table access | |||
| procedure or translation request to a different | ||||
| component. | ||||
| This event may include any or all of the | ||||
| following: | ||||
| - Terminated transactions. | ||||
| - Prefetch transactions. | ||||
| - CMOs. | ||||
| - ATOS requests. | ||||
| - HACDBS processing. | ||||
| See footnotes (1), (2), (3). |
| Event ID | Description | Notes | Mandatory | Can flter on StreamID |
|---|---|---|---|---|
| 3 | Confguration | This event is counted once when translation for | Y | Y |
| cache miss caused | an incoming transaction or translation request | |||
| by transaction or | cannot be satisfed from internal confguration | |||
| translation request | caching, and depends on a confguration table | |||
| access procedure or request to a different | ||||
| component that provides confguration | ||||
| structure access services. | ||||
| This event may include any or all of the | ||||
| following: | ||||
| - Terminated transactions. | ||||
| - Prefetch transactions. | ||||
| - CMOs. | ||||
| - ATOS requests. | ||||
| - HACDBS processing. | ||||
| See footnotes (1), (2), (3), (4). | ||||
| 4 | Translation table | External transactions performed by a | Y | Y |
| walk accesses | translation table walker, including accesses | |||
| performed speculatively. | ||||
| This applies to translation table walks | ||||
| performed for any reason including: | ||||
| - Transactions. | ||||
| - Non-ATS translation requests. | ||||
| - ATS Translation Requests. | ||||
| - ATOS requests. | ||||
| - HACDBS processing. | ||||
| - HTTU. | ||||
| - Command consumption on a DCMDQ. | ||||
| - Prefetch operations. | ||||
| 5 | Confguration | External transactions performed by a | Y | Y |
| structure access | confguration table walker, including accesses | |||
| performed speculatively. | ||||
| This includes: | ||||
| - Confguration fetches performed | ||||
| for any reason. | ||||
| - Any access to confguration | ||||
| structures caused by command | ||||
| consumption on a DCMDQ (4). | ||||
| - HACDBS processing. | ||||
| 6 | PCIe ATS | Independent of success/failure of response. | If ATS | Y |
| Translation | Note: ATS translation failures are visible at the | supported | ||
| Request received | endpoint, either through an error or because of | |||
| the endpoint causing a software-visible PRI | ||||
| Page Request. |
| Event ID | Description | Notes | Mandatory | Can flter on StreamID |
|---|---|---|---|---|
| 7 | PCIe ATS | An ATS Translated transaction was received by | If ATS | Y |
| Translated | the component. This event includes both ATS | supported | ||
| Transaction passed | Translated transactions subject to further Stage | |||
| through SMMU | 2 translation because EATS=0b10, whether | |||
| TLB/cache misses occurred or not, and those | ||||
| that bypass translation. | ||||
| This event may include terminated transactions | ||||
| (1). | ||||
| Note: Translated transactions might bypass or | ||||
| be subject to further translation, asSTE.EATS | ||||
| dictates. |
-
(1) It is IMPLEMENTATION DEFINED whether events 1, 2, 3 and 7 include transactions terminated by the SMMU. Arm recommends that terminated transactions are included in all of, or none of, events 1, 2, 3 and 7.
-
(2) For each of the following, it is IMPLEMENTATION DEFINED whether they are included in events 1, 2 and 3:
-
Speculative transactions, prefetch transactions or prefetch commands from client devices or other components.
-
ATOS requests.
-
Cache Maintenance Operations (CMOs).
Arm recommends that each of these options are either included in all of, or none of, events 1, 2 and 3.
-
(3) It is IMPLEMENTATION DEFINED if this event applies to command consumption on a DCMDQ.
-
(4) If the SID translation feature is supported, it is IMPLEMENTATION DEFINED defined whether the structures required for vSID translation are included in the configuration structures that affect Events 3 and 5.
If granule protection checks are enabled, Event IDs 2 and 4 count accesses to the GPT, when a GPT access is performed. See also: 3.25 Granule Protection Checks . The other architected PMCG events do not count accesses to the GPT. IMPLEMENTATION DEFINED events are permitted to count GPT accesses, GPT-related TLB hits or GPT-related TLB misses for the appropriate Security state.
If DPT is enabled, Event IDs 2 and 4 count DPT lookups for components that support DPT checks. See also: 3.24.3 DPT format and lookup process .
Note: In the case where the SMMU is not permitted to generate a Device Access fault based on an existing DPT TLB entry and a DPT walk is required, event 2 is counted. See also: 3.24.2.1 DPT TLB caching and Device Access faults .
PMCG events for configuration cache hits, misses and fetches for the STE lookups required by the DPT check are counted in the same manner as any other configuration-related event.
IMPLEMENTATION DEFINED events are permitted to count DPT accesses, DPT-related TLB hits or DPT-related TLB misses.
Counting of DPT lookups and accesses to the GPT is subject to the general filtering requirements in section 10.4 StreamIDs and filtering .
It is IMPLEMENTATION DEFINED whether a transaction that is retried (for any reason) is re-counted. If it is re-counted, it appears exactly like a new transaction and all relevant events are re-counted. If it is not re-counted, no counters are triggered.
When an event is mandatory, the following are both true:
-
The event is supported in at least one counter group.
-
The event is supported in as many groups as required to make the event countable for all possible StreamIDs in use.
-
Note: In a component that only caches TLB and configuration data in a single combined cache, events 2 and 3 count the same occurrence (a miss of the combined cache is a miss of both configuration and translation).
Note: As an example, a distributed implementation might have different roles for different components (and therefore different PMCGs), so that one component might translate transactions from client devices and another component handles translation requests for the former. The first component has no table walker so it is not required to count events 4 and 5. These events are instead counted by the second component, which performs configuration and translation table walks. The second component could still include TLBs and configuration caches, in which case it would also count events 2 and 3.
10.4 StreamIDs and filtering
Some event types might be filtered by StreamID, so that events are only counted if they are associated with transactions that match the configured StreamID filter. Other event types are considered unrelated to any particular StreamID and are counted by any counter that is configured to count the event (any StreamID filtering configuration is ignored). An implementation provides a StreamID filter per counter, or one StreamID filter that applies to all counters in the PMCG. This is identified through the SMMU_PMCG_CFGR.SID_FILTER_TYPE field.
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0, the StreamID filter configuration is controlled by register fields for each counter. SMMU_PMCG_EVTYPERn.{FILTER_SID_SPAN,FILTER_SEC_SID} and SMMU_PMCG_SMRn.STREAMID are associated with counter n as accessed through SMMU_PMCG_EVCNTRn.
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 1, the fields SMMU_PMCG_EVTYPER0.{FILTER_SID_SPAN, FILTER_SEC_SID} and SMMU_PMCG_SMR0.STREAMID apply to all counters in the group.
When the corresponding counter is configured to count an event type that can be filtered by StreamID, this configuration allows filtering by:
-
Exact StreamID match.
-
Partial StreamID match where a variable span of StreamID[N:0] are ignored and only upper StreamID bits are required to match the given filter.
-
Match any StreamID (filtering disabled).
There are four configuration modes for filtering events by StreamID and SEC_SID which depend on the values configured in SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN and SMMU_PMCG_SMRn.STREAMID as follows:
| Mode | Condition |
|---|---|
| ExactSID | FILTER_SID_SPAN = 0 |
| PartialSID | FILTER_SID_SPAN = 1, and STREAMID is a mask that is neither: |
| - All-ones in all implemented bits. | |
| - All-ones except for the most signifcant implemented bit. | |
| AllSIDOneSECSID | FILTER_SID_SPAN = 1, and STREAMID is a mask that is all-ones except for the |
| most-signifcant implemented bit. | |
| AllSIDManySECSID | FILTER_SID_SPAN = 1, and STREAMID is a mask that is all-ones in all implemented bits. |
When a counter uses the ExactSID mode, SMMU_PMCG_SMRn.STREAMID is programmed with a StreamID that is matched exactly. Events that are associated with other StreamIDs do not cause an increment of the counter.
When a counter uses the PartialSID mode, which allows matching a partial StreamID, where the X most-significant bits must match but the Y least-significant bits might differ, SMMU_PMCG_SMRn.STREAMID is programmed with a value that contains:
-
STREAMID[Y - 1] == 0. That is, the most significant bit in the group of bits that do not need to match is zero.
-
STREAMID[(Y - 2):0] bits are all programmed to 1 (where Y > 1).
-
The remainder of implemented bits of STREAMID (the X most-significant bits, from bit Y upwards) contain a value that will match the corresponding bits of event StreamID.
-
Examples (in binary):
- 0000:0000:0001:1011:1111:0111:1111:0111 matches 0000:0000:0001:1011:1111:0111:1111:xxxx
-
0000:0000:0001:1011:1111:0111:1111:0110 matches 0000:0000:0001:1011:1111:0111:1111:011x
-
0000:0000:0001:1011:1111:0101:1111:1111 matches
-
0000:0000:0001:1011:1111:01xx:xxxx:xxxx
The AllSIDOneSECSID mode, which allows matching all the StreamIDs of one Security state, is a particular case of the PartialSID mode, where Y is equal to SMMU_IDR0.SIDSIZE.
When a counter uses the AllSIDManySECSID mode, which matches any StreamID regardless of its Security state, SMMU_PMCG_SMRn.STREAMID is programmed with 1 for all implemented bits:
-
Note: The STREAMID field might implement fewer bits than the SMMU StreamID size. Arm recommends that 0xFFFFFFFF is written to this field to ensure that all implemented bits are set without first determining how many bits to write.
-
Note: A value with 0 in the most-significant implemented bit and 1 in all bits below that point is an alternative encoding that matches any StreamID. This is the maximum mask given the encoding of the variable mask size, but requires knowledge of the implemented field size. When Secure state is supported, this encoding behaves differently to the “all 1” encoding in terms of the scope of filtering according to SEC_SID.
When the PMCG implements support for Secure state (see section 10.6 Support for Secure state ):
-
The SMMU_PMCG_EVTYPERn.FILTER_SEC_SID flag determines whether the StreamID filter configuration (as determined by SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN and SMMU_PMCG_SMRn.STREAMID) applies to the Secure or the Non-secure StreamID namespace. Secure observation can be disabled so that StreamID matching can only match events that are associated with Non-secure StreamIDs, overriding the effective value of this flag.
-
When SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN == 1 and SMMU_PMCG_SMRn.STREAMID field is programmed with 1 in all implemented bits, the filter matches all StreamIDs for both Secure and Non-secure namespaces if Secure observation is enabled, and matches all Non-secure StreamIDs if Secure observation is not enabled. In SMMUv3.0, it is IMPLEMENTATION DEFINED whether:
-
The filter matches all StreamIDs in one of the Secure or Non-secure namespaces as determined by the effective value of the SMMU_PMCG_EVTYPERn.FILTER_SEC_SID flag.
-
The filter matches all StreamIDs for both Secure and Non-secure namespaces if Secure observation is enabled, and matches all Non-secure StreamIDs if Secure observation is not enabled.
-
-
When SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN == 1 and SMMU_PMCG_SMRn.STREAMID is programmed with 0 in the most-significant implemented bit and 1 in all other implemented bits, the filter matches all StreamIDs for the Secure or the Non-secure namespace as determined by the effective value of the SMMU_PMCG_EVTYPERn.FILTER_SEC_SID flag.
When PMCG implements support for Realm state, in ExactSID, PartialSID and AllSIDOneSECSID modes, StreamID filtering is applied, and SEC_SID filtering is applied as described in the table below, where Rel and Sec are defined as:
-
Rel = SMMU_PMCG_EVTYPERn.FILTER_REALM_SID & SMMU_PMCG_ROOTCR.RLO;
-
Sec = SMMU_PMCG_EVTYPERn.FILTER_SEC_SID & SMMU_PMCG_SCR.SO;
| Rel | Sec | Result |
|---|---|---|
| 0 | 0 | Count only Non-secure events. |
| 0 | 1 | Count only Secure events. |
| 1 | 0 | Count only Realm events. |
| 1 | 1 | Reserved, behaves as {0, 0}. |
When PMCG implements support for Realm state, in AllSIDManySECSID mode, StreamID
filtering is not applied and SEC_SID filtering is applied as follows, according to the values of SMMU_PMCG_EVTYPERn.{FILTER_REALM_SID, FILTER_SEC_SID}, SMMU_PMCG_SCR.SO and SMMU_PMCG_ROOTCR.{RTO, RLO, SAO}:
If FILTER_REALM_SID = 0 then:
-
Non-secure events are counted.
-
If SO = 1 then Secure events are additionally counted.
If FILTER_REALM_SID = 1 then:
-
If FILTER_SEC_SID = 0 then:
-
Non-secure events are counted.
-
If RLO = 1 then Realm events are additionally counted.
-
-
If FILTER_SEC_SID = 1 then:
-
Non-secure events are counted.
-
If SO = 1 then Secure events are additionally counted.
-
If RLO = 1 then Realm events are additionally counted.
-
If RTO = 1 then NoStreamID accesses to Root PA space are additionally counted.
-
If SAO = 1 then NoStreamID accesses to SA PA space are additionally counted.
-
For the purposes of counting events for NoStreamID accesses, the Security state of the access is defined as follows:
-
If the target PA space of the access is NS, Realm, Secure, SA or Root, then it is treated as conveying the Security state of the access.
-
Otherwise (including if the target PA space of the access is NSP), then the Security state is Non-secure.
Accesses with the PM attribute are counted in the same manner as accesses without the PM attribute, with the exception that accesses with PM = 1 are counted only if SMMU_PMCG_ROOTCR.PMO = 1.
Note: This applies to any access with PM = 1, regardless of the output PA space. See section 3.25.10.1.1 Protected Mode .
10.4.1 Counter Group StreamID size
The StreamID that is handled by a PMCG is not required to be the full SMMU-architectural StreamID as seen by the SMMU programming interface. This arises from the possibility that a PMCG represents a sub-component of the SMMU and, in a distributed implementation, the component might only service a subset of the StreamID space of the SMMU. In such an implementation, the upper bits of StreamID might be considered fixed for a given sub-component. For example, block 0 serves clients with StreamIDs 0x00 to 0x0F and block 1 serves clients with StreamIDs 0x10 to 0x1F.
In all cases, the low-order PMCG StreamID bits [N:0] must be equivalent to the SMMU StreamID[N:0]. Where a PMCG StreamID filter is programmed, SMMU_PMCG_SMRn.STREAMID might implement fewer bits than indicated by SMMU_IDR1.SIDSIZE in the SMMU with which the PMCG is associated. The implemented size of the SMMU_PMCG_SMRn.STREAMID field is IMPLEMENTATION DEFINED. The association between the span of StreamIDs served by a given PMCG and the overall SMMU StreamID namespace is IMPLEMENTATION DEFINED.
For example, an SMMU with a 17-bit StreamID might be composed of two components A and B, which support client devices with StreamIDs 0 to 0xFFFF and 0x10000 to 0x1FFFF respectively. In order to count events from the client device with StreamID 0x12345, software programs a counter in the PMCG that is associated with component B to filter on StreamID 0x12345. However, SMMU_PMCG_SMRn.STREAMID might only implement 16 bits and read back the value 0x02345.
Software must not depend on readback of SMMU_PMCG_SMRn.STREAMID returning the full SMMU StreamID. The readback value might be truncated to the PMCG StreamID size.
10.4.2 Counting of NoStreamID accesses
NoStreamID accesses are permitted to cause events to be counted, subject to all of the following constraints:
-
For the purposes of PMCG filtering, the Security state of a NoStreamID access is defined as follows: – If the target PA space of the access is NS, Realm, Secure, SA or Root, then it is treated as conveying the Security state of the access. Note: If the target PA space of the access is SA, then the access is counted only in AllSIDManySECSID mode, subject to the value of SMMU_PMCG_ROOTCR.SAO. See section 3.25.10 Granular Data Isolation .
- Otherwise (including if the target PA space of the access is NSP), then the Security state is Non-secure.
-
NoStreamID accesses are only counted if counting of events for their effective Security state is enabled.
-
NoStreamID accesses are only counted if SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN == 1, and SMMU_PMCG_SMRn.STREAMID is programmed to count accesses from all streams, and that selection of all streams includes the effective Security state of the NoStreamID accesses. Note: This is when SMMU_PMCG_SMRn.STREAMID is all-ones in all implemented bits, or all-ones in all implemented bits except for the most-significant bit.
-
NoStreamID accesses to the NSP PA space are counted in the same manner as NoStreamID accesses to the NS PA space, with the exception that such accesses are counted only if SMMU_PMCG_ROOTCR.PMO is 1.
Note: These requirements mean that if FILTER_REALM_SID is zero, or not implemented, then no PMCG events are counted for accesses from NoStreamID devices to Root or Realm physical address spaces.
When a NoStreamID access is permitted to cause events to be counted, then it can count:
-
Event ID 1 for the NoStreamID transaction.
-
Event IDs 2 and 4 for the GPT-related events, as described in section 10.3 Monitor events .
-
IMPLEMENTATION DEFINED GPT-related events.
See also:
- 3.25.1.1 GPC for client devices without a StreamID .
10.4.3 PARTID- and PMG-based filtering
If SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1, then the PMCG supports filtering of events by MPAM PARTID and PMG.
When PARTID- or PMG-based filtering is enabled in a particular SMMU_PMCG_EVTYPERn register, the SMMU PMCG uses the PARTID and/or PMG values configured in the corresponding SMMU_PMCG_SMRn register to filter events that are counted in the corresponding SMMU_PMCG_EVTYPERn register.
Filtering by PARTID and PMG can be enabled independently, using the configuration bits SMMU_PMCG_EVTYPERn.{FILTER_PARTID, FILTER_PMG, FILTER_MPAM_NS}.
In an SMMU implementation with RME DA, SMMU_PMCG_EVTYPERn.FILTER_MPAM_NS is replaced by a 2-bit field, FILTER_MPAM_SP. This change is architected such that the values of FILTER_MPAM_NS directly match the first two values of FILTER_MPAM_SP. See SMMU_PMCG_EVTYPERn.
If filtering by PARTID and/or PMG is enabled, then filtering by StreamID is not available.
When filtering by PARTID, the SMMU compares the PARTID value configured in SMMU_PMCG_SMRn to the output PARTID of each transaction or SMMU-originated access, whether that comes from SMMU_(S_)GBPMPAM, SMMU_(*_)GMPAM, the STE or the CD.
When filtering by PMG, the SMMU compares the PMG value configured in SMMU_PMCG_SMRn to the output PMG of each transaction or SMMU-originated access, whether that comes from SMMU_(S_)GBPMPAM, the STE or the CD.
It is IMPLEMENTATION DEFINED whether an SMMU PMCG can filter events 3 and 5 by PARTID and PMG.
For each IMPLEMENTATION DEFINED event, it is IMPLEMENTATION DEFINED whether an SMMU PMCG can filter that event by PARTID and PMG.
If an SMMU PMCG is configured to filter an event by PARTID or PMG and the SMMU does not support filtering by PARTID or PMG for that event ID, the event is counted without filtering.
Note: If filtering by PARTID or PMG is supported and enabled for an event ID and a transaction is terminated before it was assigned with a PARTID and PMG then it is IMPLEMENTATION DEFINED if an event arising from that transaction is counted.
If an SMMU PMCG is configured to filter a filterable event by PARTID or PMG values exceeding those advertised in SMMU_PMCG_(S_)MPAMIDR, it counts no events.
| Event ID | Description | Can flter by PARTID or PMG |
|---|---|---|
| 0 | Clock cycle | No |
| 1 | Transaction or request | Yes |
| 2 | TLB miss caused by incoming transaction or | Yes |
| translation request | ||
| 3 | Confguration cache miss caused by transaction or | IMPLEMENTATION DEFINED |
| translation request | ||
| 4 | Translation table walk access | Yes |
| 5 | Confguration structure access | IMPLEMENTATION DEFINED |
| 6 | PCIe ATS Translation Request received | Yes |
| 7 | PCIe ATS Translated Transaction passed through | Yes |
| SMMU |
10.4.4 Counting of non-attributable events
A non-attributable event is an event that is not directly associated with a single Security state, but might reveal information about a Security state.
Note: None of the architected SMMUv3 events are non-attributable events.
If Realm state is not implemented and Secure state is implemented, non-attributable events are only counted if SMMU_PMCG_SCR.SO is 1.
If the Realm programming interface is present, then non-attributable events are only counted if all of the following are true:
-
SMMU_PMCG_ROOTCR.NAO is 1.
-
Either or both of SMMU_PMCG_SCR.SO and SMMU_PMCG_SCR.NAO are 1.
10.5 Registers
The total number of counter groups that are associated with one SMMU is IMPLEMENTATION DEFINED. Each counter group is represented by one 4KB page (Page 0) with one optional additional 4KB page (Page 1), both of which are at IMPLEMENTATION DEFINED base addresses.
If Page 1 is present, the registers for counter values, overflow status and shadow capture control appear in Page 1 instead of Page 0. Presence is indicated by SMMU_PMCG_CFGR.RELOC_CTRS. Arm recommends that Page 1 is implemented and, if so, Arm strongly recommends that Page 1 is located within an aligned 64KB system address span that is otherwise unused.
Note: This permits a hypervisor to use a 64KB stage 2 granule to expose the Page 1 counter values for direct access by a virtual machine. Arm expects that guest access to stage 1 registers (for counter configuration) will be trapped and controlled by the hypervisor, rather than accessed directly.
Access behaviors follow the same rules as for the SMMU registers described in section 6.2 Register overview . In particular:
-
Aligned 32-bit access is permitted to 64-bit registers.
-
It is IMPLEMENTATION DEFINED whether 64-bit accesses to 64-bit registers are atomic.
-
All registers are little-endian.
Unless otherwise specified, software is permitted to read or write a register at any time. Writes to read-only registers are IGNORED.
10.5.1 SMMU_PMCGn address map
The map of the base PMCG register Page 0 is shown here:
| Offset | Register | Notes |
|---|---|---|
| 0x000 | SMMU_PMCG_EVCNTRn | 32- or 64-bit, RW, 0 <= n < 64 |
| + | Registers placed on a 4-byte stride if | |
| stride*n | SMMU_PMCG_CFGR.SIZE <= 31 (counters 32-bit or smaller), | |
| (0x000 | otherwise an 8-byte stride. | |
| to | ||
| 0x1FF) | ||
| 0x400 | SMMU_PMCG_EVTYPERn | 32-bit, RW, 0 <= n < 64 |
| + 4*n | ||
| (0x400 | ||
| to | ||
| 0x4FF) | ||
| 0x600 | SMMU_PMCG_SVRn | 32- or 64-bit, RO, 0 <= n < 64 |
| + | Stride same as forSMMU_PMCG_EVCNTRn. | |
| stride*n | ||
| (0x600 | ||
| to | ||
| 0x7FF) | ||
| 0xA00 | SMMU_PMCG_SMRn | 32-bit, RW, 0 <= n < 64 |
| + 4*n | ||
| (0xA00 | ||
| to | ||
| 0xAFF) |
| Offset | Register | Notes |
|---|---|---|
| 0xC00 | SMMU_PMCG_CNTENSET0 | 64-bit, RW |
| 0xC20 | SMMU_PMCG_CNTENCLR0 | 64-bit, RW |
| 0xC40 | SMMU_PMCG_INTENSET0 | 64-bit, RW |
| 0xC60 | SMMU_PMCG_INTENCLR0 | 64-bit, RW |
| 0xC80 | SMMU_PMCG_OVSCLR0 | 64-bit, RW |
| 0xCC0 | SMMU_PMCG_OVSSET0 | 64-bit, RW |
| 0xD88 | SMMU_PMCG_CAPR | 32-bit, WO |
| 0xDF8 | SMMU_PMCG_SCR | 32-bit, Secure, RW |
| 0xE00 | SMMU_PMCG_CFGR | 32-bit, RO |
| 0xE04 | SMMU_PMCG_CR | 32-bit, RW |
| 0xE08 | SMMU_PMCG_IIDR | 32-bit, RO |
| 0xE20 | SMMU_PMCG_CEID0 | 64-bit, RO |
| 0xE28 | SMMU_PMCG_CEID1 | 64-bit, RO |
| 0xE40 | Alias ofSMMU_PMCG_SCR, otherwise | 32-bit, Secure, RW |
| RAZ/WI | ||
| 0xE48 | SMMU_PMCG_ROOTCR | 32-bit, Root, RW |
| 0xE50 | SMMU_PMCG_IRQ_CTRL | 32-bit, RW |
| 0xE54 | SMMU_PMCG_IRQ_CTRLACK | 32-bit, RO |
| 0xE58 | SMMU_PMCG_IRQ_CFG0 | 64-bit, RW |
| 0xE60 | SMMU_PMCG_IRQ_CFG1 | 32-bit, RW |
| 0xE64 | SMMU_PMCG_IRQ_CFG2 | 32-bit, RW |
| 0xE68 | SMMU_PMCG_IRQ_STATUS | 32-bit, RO |
| 0xE6C | SMMU_PMCG_GMPAM | 32-bit, RW |
| 0xE70 | SMMU_PMCG_AIDR | 32-bit, RO |
| 0xE74 | SMMU_PMCG_MPAMIDR | 32-bit, RO |
| 0xE78 | SMMU_PMCG_S_MPAMIDR | 32-bit, Secure, RO |
| Offset | Register | Notes |
|---|---|---|
| 0xE80 | IMPLEMENTATION DEFINED | |
| - | ||
| 0xEFF | ||
| 0xFB0 | SMMU_PMCG_ID_REGS | IMPLEMENTATION DEFINED |
| - | ||
| 0xFFF | ||
| When Page 1 is present (SMMU_PMCG_CFGR.RELOC_CTRS == 1), the following registers are relocated to | ||
| Page 1 and their corresponding Page 0 locations become RES0. Offsets are shown relative to the base address of | ||
| Page 1. | ||
| Offset | Register | Notes |
| 0x000 + | SMMU_PMCG_EVCNTRn | Same as for corresponding locations in Page 0. |
| n*stride | ||
| (0x000 | ||
| to | ||
| 0x1FF) | ||
| 0x600 + | SMMU_PMCG_SVRn | |
| n*stride | ||
| (0x600 | ||
| to | ||
| 0x7FF) | ||
| 0xC80 | SMMU_PMCG_OVSCLR0 | |
| 0xCC0 | SMMU_PMCG_OVSSET0 | |
| 0xD88 | SMMU_PMCG_CAPR |
10.5.2 Register details
10.5.2.1 SMMU_PMCG_EVCNTR<n>, n = 0 - 63
The SMMU_PMCG_EVCNTR<n> characteristics are:
Purpose
Provides Counters for PMCG events.
Configuration
When counter size is <= 32 bits (SMMU_PMCG_CFGR.SIZE <= 31), these registers are 32 bits in size. Otherwise, these registers are 64 bits in size. Present in an array of n registers, all of size 32 or 64, each corresponding to counter n.
The counter value is incremented when an event matching SMMU_PMCG_EVTYPERn.EVENT occurs, the counter is enabled (the respective CNTEN == 1) and, if the event type is filterable by StreamID, filters match. See section 10.4 StreamIDs and filtering for information on filtering.
When a counter value is incremented by the PMCG, the increment is atomic with respect to external writes to this register.
Registers corresponding to unimplemented counters are RES0.
Attributes
SMMU_PMCG_EVCNTR<n> is a:
-
32-bit register when UInt(SMMUv3_PMCG.SMMU_PMCG_CFGR.SIZE) <= 31.
-
64-bit register when UInt(SMMUv3_PMCG.SMMU_PMCG_CFGR.SIZE) > 31.
This register is part of the SMMUv3_PMCG block.
Field descriptions
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) <= 31:
31 0
COUNTER_VALUE
COUNTERVALUE, bits [31:0]
Counter value[N:0].
R == SMMU_PMCG_CFGR.SIZE + 1.
If R < 32, bits [31:R] are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) > 31:
| 63 | 32 | |
|---|---|---|
| COUNTER_VALUE | ||
| 31 | 0 | |
| COUNTER_VALUE |
COUNTERVALUE, bits [63:0]
Counter value[N:0].
- R == SMMU_PMCG_CFGR.SIZE + 1.
If R > 32 and R < 64, bits [63:R] are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Accessing SMMUPMCGEVCNTR<n>
Accesses to this register use the following encodings:
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) <= 31
Accessible at offset 0x000 + (4 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) > 31
Accessible at offset 0x000 + (8 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.2 SMMU_PMCG_EVTYPER<n>, n = 0 - 63
The SMMU_PMCG_EVTYPER<n> characteristics are:
Purpose
These registers contain per-counter configuration, in particular the event type counted.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_EVTYPER<n> is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 30 29 28 27 20 19 18 17 16 15 0
RES0 EVENT
OVFCAP FILTER_PARTID
FILTER_SEC FILTER_PMG
_SID FILTER_MPAM_SP
FILTER_SID_SP FILTER_REALM_SID
AN
OVFCAP, bit [31]
When SMMUPMCGCFGR.CAPTURE == 1:
Overflow capture.
| OVFCAP | Meaning |
|---|---|
| 0b0 | An overfow of counter n does not trigger a capture of all counters. |
| 0b1 | An overfow of counter n triggers a capture of all counters in the same way as by |
| SMMU_PMCG_CAPR.CAPTURE. |
The reset behavior of this field is:
• This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
FILTERSECSID, bit [30]
When n == 0 or SMMUPMCGCFGR.SIDFILTERTYPE == 0:
Filter Secure StreamIDs.
| FILTER_SEC_SID | Meaning |
|---|---|
| 0b0 | Count events originating from Non-secure |
| StreamIDs. | |
| 0b1 | Count events originating from Secure |
| StreamIDs. |
-
This bit is RES0 if the PMCG does not implement support for Secure state. Otherwise, this bit is effectively 0 if support for Secure state is implemented but Secure observation is disabled (SMMU_PMCG_SCR.SO == 0).
-
For event types that can be filtered on StreamID, this bit is considered in conjunction with FILTER_SID_SPAN and SMMU_PMCG_SMRn.STREAMID to determine how filtering is applied, based on StreamID and SEC_SID. See section 10.4 StreamIDs and filtering .
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
FILTERSIDSPAN, bit [29]
When n == 0 or SMMUPMCGCFGR.SIDFILTERTYPE == 0:
Filter StreamID.
| FILTER_SID_SPAN | Meaning |
|---|---|
| 0b0 | SMMU_PMCG_SMRn.STREAMID flters event on an exact |
| StreamID match, if the event type can be fltered on StreamID. | |
| 0b1 | TheSMMU_PMCG_SMRn.STREAMID feld encodes a match |
| span of StreamID values. See 10.4_StreamIDs and fltering_. |
Note: The span can encode ALL, equivalent to disabling filtering on StreamID. The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
FILTERREALMSID, bit [28]
When SMMU_PMCG_ROOTCR.ROOTCR_IMPL == 1 and (n == 0 or SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0):
Count events relating to Realm StreamIDs.
| FILTER_REALM_SID | Meaning |
|---|---|
| 0b0 | Do not count events relating to Realm |
| StreamIDs. | |
| 0b1 | Count events relating to Realm |
| StreamIDs. |
If SMMU_PMCG_ROOTCR.RLO is 0, this bit is treated as 0 for all purposes other than read back of the bit value.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
Bits [27:20]
Reserved, RES0.
FILTERMPAMSP, bits [19:18]
When SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1 and (n == 0 or SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0):
Select MPAM_SP for SMMU_PMCG_SMRn.{PARTID, PMG}.
SMMU_PMCG_SMRn.{PARTID, PMG} are treated as belonging to the following PARTID spaces:
| FILTER_MPAM_SP | Meaning |
|---|---|
| 0b00 | IfSMMU_PMCG_SCR.SO is 1 then Secure. Otherwise |
| treated as 0b01. | |
| 0b01 | Non-secure. |
| 0b10 | Reserved, behaves as 0b00. |
| 0b11 | IfSMMU_PMCG_ROOTCR.RLO is 1 then Realm. Otherwise |
| treated as 0b01. |
If SMMU_PMCG_ROOTCR.ROOTCR_IMPL = 0 then bit [19] is RES0, and bit [18] selects only between Non-secure and Secure PARTID space.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
FILTERPMG, bit [17]
When SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1 and (n == 0 or SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0):
Filter events by the value specified in SMMU_PMCG_SMRn.PMG.
| FILTER_PMG | Meaning |
|---|---|
| 0b0 | Events are not fltered by PMG. |
| 0b1 | Only count events associated with the PMG specifed in |
| SMMU_PMCG_SMRn.PMG. |
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
FILTERPARTID, bit [16]
When SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1 and (n == 0 or SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0):
Filter events by the value specified in SMMU_PMCG_SMRn.PARTID.
| FILTER_PARTID | Meaning |
|---|---|
| 0b0 | Events are not fltered by PARTID. |
| 0b1 | Only count events associated with the PARTID specifed in |
| SMMU_PMCG_SMRn.PARTID. |
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
Reserved, RES0.
EVENT, bits [15:0]
Event.
-
Event type that causes this counter to increment.
-
An IMPLEMENTATION DEFINED number of low-order bits of this register are implemented, unimplemented upper bits are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Additional Information
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0, the field FILTER_SID_SPAN and, if Secure state is supported, FILTER_SEC_SID, are present in every implemented SMMU_PMCG_EVTYPERn register and correspond to counter SMMU_PMCG_EVCNTRn for all implemented values of n.
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 1, these fields are present only in SMMU_PMCG_EVTYPER0 and the FILTER_SID_SPAN and FILTER_SEC_SID fields in SMMU_PMCG_EVTYPERx, for x >= 1, are RES0.
The same relationship with SMMU_PMCG_CFGR.SID_FILTER_TYPE applies to FILTER_PARTID, FILTER_PMG and FILTER_MPAM_NS.
See SMMU_PMCG_SMRn and 10.4 StreamIDs and filtering for information on StreamID filtering. When filtering is enabled, an event is counted only if it matches the filter conditions for the counter.
Note: Event types that cannot be filtered on StreamID are always counted, as they cannot be filtered out using FILTER_* configuration.
If FILTER_PARTID == 1 or FILTER_PMG == 1, FILTER_SID_SPAN is IGNORED and events are not filtered by StreamID.
If FILTER_PARTID == 0 and FILTER_PMG == 0, FILTER_MPAM_NS is IGNORED.
See SMMU_PMCG_SMRn and 10.4.3 PARTID- and PMG-based filtering for information on PARTIDand PMG-based filtering. When filtering is enabled, an event is counted only if it matches the filter conditions for the counter.
Note: Event types that cannot be filtered on PARTID and PMG are always counted, as they cannot be filtered out using FILTER_* configuration.
Registers corresponding to unimplemented counters are RES0.
Accessing SMMUPMCGEVTYPER<n>
Accesses to this register use the following encodings:
Accessible at offset 0x400 + (4 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.3 SMMU_PMCG_SVR<n>, n = 0 - 63
The SMMU_PMCG_SVR<n> characteristics are:
Purpose
PMCG Shadow value, 0 <= n < 64.
Configuration
When counter size is <= 32 bits (SMMU_PMCG_CFGR.SIZE <= 31), these registers are 32 bits in size. Otherwise, these registers are 64 bits in size. Present in an array of registers (all of size 32 or 64) each corresponding to counter n.
When counter value capture is implemented (SMMU_PMCG_CFGR.CAPTURE == 1), these registers hold the captured counter values of the corresponding entries in SMMU_PMCG_EVCNTRn. Registers corresponding to unimplemented counters are RES0.
If counter value capture is not implemented (SMMU_PMCG_CFGR.CAPTURE == 0), all SMMU_PMCG_SVRn registers are RES0.
This register is present only when SMMU_PMCG_CFGR.CAPTURE == 1. Otherwise, direct accesses to SMMU_PMCG_SVR<n> are RES0.
Attributes
SMMU_PMCG_SVR<n> is a:
-
32-bit register when UInt(SMMUv3_PMCG.SMMU_PMCG_CFGR.SIZE) <= 31.
-
64-bit register when UInt(SMMUv3_PMCG.SMMU_PMCG_CFGR.SIZE) > 31.
This register is part of the SMMUv3_PMCG block.
Field descriptions
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) <= 31:
31 0
SHADOW_COUNTER_VALUE
SHADOWCOUNTERVALUE, bits [31:0]
Shadow counter value[N:0].
R == SMMU_PMCG_CFGR.SIZE + 1.
If R < 32, bits [31:R-1] are RES0. The reset behavior of this field is:
- This field resets to an UNKNOWN value.
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) > 31:
| 63 | 32 | |
|---|---|---|
| SHADOW_COUNTER_VALUE | ||
| 31 | 0 | |
| SHADOW_COUNTER_VALUE |
SHADOWCOUNTERVALUE, bits [63:0]
Shadow counter value[N:0].
R == SMMU_PMCG_CFGR.SIZE + 1.
If R > 32 and R < 64, bits [63:R-1] are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Accessing SMMUPMCGSVR<n>
Accesses to this register use the following encodings:
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) <= 31
Accessible at offset 0x600 + (4 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
When UInt(SMMUv3PMCG.SMMUPMCGCFGR.SIZE) > 31
Accessible at offset 0x600 + (8 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.4 SMMU_PMCG_SMR<n>, n = 0 - 63
The SMMU_PMCG_SMR<n> characteristics are:
Purpose
PMCG Counter stream match filter, 0 <= n < 64.
Configuration
This register is present only when n == 0 or SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0. Otherwise, direct accesses to SMMU_PMCG_SMR<n> are RES0.
Attributes
SMMU_PMCG_SMR<n> is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
When SMMUv3_PMCG.SMMU_PMCG_EVTYPER<n>.FILTER_PARTID == ‘1’ or SMMUv3_PMCG.SMMU_PMCG_EVTYPER<n>.FILTER_PMG == ‘1’:
| 31 24 23 16 15 0 | 31 24 23 16 15 0 | 31 24 23 16 15 0 |
|---|---|---|
| RES0 | PMG | PARTID |
Filtering by MPAM PARTID and/or PMG values occurs.
Filtering by StreamID does not occur.
See section 10.4.3 PARTID- and PMG-based filtering .
Bits [31:24]
Reserved, RES0.
PMG, bits [23:16]
PMG value by which PMCG filters events.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
PARTID, bits [15:0]
PARTID value by which PMCG filters events.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Otherwise:
| 31 | 0 | |
|---|---|---|
| STREAMID |
STREAMID, bits [31:0]
-
When the corresponding SMMU_PMCG_EVTYPERn.EVENT indicates an event that cannot be filtered on StreamID, the value in this field is IGNORED.
-
Otherwise:
-
When the corresponding SMMU_PMCG_EVTYPERn.FILTER_SID_SPAN == 0, the respective counter only counts events associated with a StreamID matching this field exactly.
-
When FILTER_SID_SPAN == 1, this field encodes a mask value that allows a span of least-significant StreamID bits to be ignored for the purposes of filtering on a StreamID match. When all implemented bits of this field are written to 1, any StreamID is matched. See section 10.4 StreamIDs and filtering .
-
When Secure observation is enabled, SMMU_PMCG_EVTYPERn.FILTER_SEC_SID determines whether the StreamID is matched from Secure or Non-secure StreamID spaces, see section 10.4 StreamIDs and filtering for the behavior of the match-all encodings with respect to Secure/Non-secure namespaces.
-
-
This field implements an IMPLEMENTATION DEFINED number of contiguous bits (from 0 upwards) corresponding to the PMCG StreamID size, see section 10.4.1 Counter Group StreamID size . Bits outside this range read as zero, writes ignored (RAZ/WI).
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Additional Information for Otherwise
These registers contain StreamID-match configuration for filtering events on StreamID.
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 0, each SMMU_PMCG_SMRn corresponds to counter SMMU_PMCG_EVCNTRn for all implemented values of n.
When SMMU_PMCG_CFGR.SID_FILTER_TYPE == 1, SMMU_PMCG_SMR0 applies to all counters in the group and registers SMMU_PMCG_SMRx for x >= 1 are RES0.
See section 10.4 StreamIDs and filtering for more information on StreamIDs in PMCGs.
Note: To count events for a given StreamID, software must choose a counter in the appropriate counter group to use for the required event type (which is determined in an IMPLEMENTATION DEFINED manner) and then write the full StreamID value into the STREAMID field of this register.
Registers corresponding to unimplemented counters are RES0.
Accessing SMMUPMCGSMR<n>
Accesses to this register use the following encodings:
Accessible at offset 0xA00 + (4 * n) from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.5 SMMU_PMCG_CNTENSET0
The SMMU_PMCG_CNTENSET0 characteristics are:
Purpose
Counter enable, SET.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CNTENSET0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| CNTEN | ||
| 31 | 0 | |
| CNTEN |
CNTEN, bits [63:0]
Counter enable.
64-bit register containing a bitmap of per-counter enables.
Bit CNTEN[n] corresponds to counter n, which is enabled if CNTEN[n] == 1 and SMMU_PMCG_CR.E == 1.
Write 1 to a bit location to set the per-counter enable.
Reads return the state of enables.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1S.
Accessing SMMUPMCGCNTENSET0
Accesses to this register use the following encodings:
Accessible at offset 0xC00 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.6 SMMU_PMCG_CNTENCLR0
The SMMU_PMCG_CNTENCLR0 characteristics are:
Purpose
Counter enable, CLEAR.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CNTENCLR0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| CNTEN | ||
| 31 | 0 | |
| CNTEN |
CNTEN, bits [63:0]
Counter enable.
Bitmap indexed similar to SMMU_PMCG_CNTENSET0.
Write 1 to a bit location to clear the per-counter enable.
Reads return the state of enables.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1C.
Accessing SMMUPMCGCNTENCLR0
Accesses to this register use the following encodings:
Accessible at offset 0xC20 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.7 SMMU_PMCG_INTENSET0
The SMMU_PMCG_INTENSET0 characteristics are:
Purpose
Counter interrupt contribution enable, SET.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_INTENSET0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| INTEN | ||
| 31 | 0 | |
| INTEN |
INTEN, bits [63:0]
Per counter interrupt enable.
Bitmap indexed similar to SMMU_PMCG_CNTENSET0.
Write 1 to a bit location to set the per-counter interrupt enable.
Reads return the state of interrupt enables.
Overflow of counter n triggers a PMCG interrupt if, at the time that the overflow occurs, the corresponding INTEN[n] == 1 && SMMU_PMCG_IRQ_CTRL.IRQEN == 1.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1S.
Accessing SMMUPMCGINTENSET0
Accesses to this register use the following encodings:
Accessible at offset 0xC40 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.8 SMMU_PMCG_INTENCLR0
The SMMU_PMCG_INTENCLR0 characteristics are:
Purpose
Counter interrupt contribution enable CLEAR.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_INTENCLR0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| INTEN | ||
| 31 | 0 | |
| INTEN |
INTEN, bits [63:0]
Per counter interrupt enable.
Bitmap indexed similar to SMMU_PMCG_CNTENSET0.
Write 1 to a bit location to clear the per-counter interrupt enable.
Reads return the state of interrupt enables.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1C.
Accessing SMMUPMCGINTENCLR0
Accesses to this register use the following encodings:
Accessible at offset 0xC60 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.9 SMMU_PMCG_OVSCLR0
The SMMU_PMCG_OVSCLR0 characteristics are:
Purpose
Overflow status, CLEAR.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_OVSCLR0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| OVS | ||
| 31 | 0 | |
| OVS |
OVS, bits [63:0]
Overflow counter status.
Bitmap indexed similar to SMMU_PMCG_CNTENSET0.
Write 1 to a bit location to clear the per-counter overflow status.
Reads return the state of overflow status.
Overflow of counter n (a transition past the maximum unsigned value of the counter causing the value to become, or pass, zero) sets the corresponding OVS[n] bit.
In addition, this event can trigger the PMCG interrupt and cause a capture of the PMCG counter values (see SMMU_PMCG_EVTYPERn.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1C.
Accessing SMMUPMCGOVSCLR0
Accesses to this register use the following encodings:
Accessible at offset 0xC80 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.10 SMMU_PMCG_OVSSET0
The SMMU_PMCG_OVSSET0 characteristics are:
Purpose
Overflow status, SET.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_OVSSET0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| OVS | ||
| 31 | 0 | |
| OVS |
OVS, bits [63:0]
Overflow counter status.
Bitmap indexed similar to SMMU_PMCG_CNTENSET0.
Write 1 to a bit location to set the per-counter overflow status.
Reads return the state of overflow status.
Software setting an OVS bit is similar to an OVS bit becoming set because of a counter overflow, except it is IMPLEMENTATION SPECIFIC whether enabled overflow side effects of triggering the PMCG interrupt or causing a capture of the PMCG counter values are performed.
High-order bits of the bitmap beyond the number of implemented counters that is specified in (SMMU_PMCG_CFGR.NCTR + 1) are RES0.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Access to this field is W1S.
Accessing SMMUPMCGOVSSET0
Accesses to this register use the following encodings:
Accessible at offset 0xCC0 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.11 SMMU_PMCG_CAPR
The SMMU_PMCG_CAPR characteristics are:
Purpose
Counter shadow value capture.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CAPR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 1 0
RES0
CAPTURE
Bits [31:1]
Reserved, RES0.
CAPTURE, bit [0]
Capture.
-
When counter capture is supported (SMMU_PMCG_CFGR.CAPTURE == 1), a write of 1 to this bit triggers a capture of all SMMU_PMCG_EVCNTRn values within the PMCG into their respective SMMU_PMCG_SVRn shadow register.
-
This register reads as zero.
-
When SMMU_PMCG_CFGR.CAPTURE == 0, this field is RES0.
The reset behavior of this field is:
- This field resets to ‘0’.
Accessing SMMUPMCGCAPR
Accesses to this register use the following encodings:
Accessible at offset 0xD88 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are WO.
10.5.2.12 SMMU_PMCG_SCR
The SMMU_PMCG_SCR characteristics are:
Purpose
PMCG Secure control register.
Configuration
This register is present only when the PMCG supports Secure state. Otherwise, direct accesses to SMMU_PMCG_SCR are RES0.
Attributes
SMMU_PMCG_SCR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 30 5 4 3 2 1 0
1 RES0 NAO SO
READS_AS_ONE MSI_MPAM_NS NSRA
NSMSI
READSASONE, bit [31]
READS_AS_ONE Meaning 0b1 Secure software can use READS_AS_ONE to discover support for Secure state in the PMCG.
Access to this field is RO.
Bits [30:5]
Reserved, RES0.
NAO, bit [4]
When SMMUPMCGROOTCR.ROOTCRIMPL == 1:
Permit counting of events not attributable to a specific Security state.
| NAO | Meaning |
|---|---|
| 0b0 | Counting non-attributable events is prevented. |
| 0b1 | Counting non-attributable events is not prevented by this bit. |
See also:
- 10.4.4 Counting of non-attributable events .
The reset behavior of this field is:
- This field resets to ‘0’.
Otherwise:
Reserved, RES0.
MSIMPAMNS, bit [3]
When SMMUPMCGSMPAMIDR.HASMPAMNS == 1:
| MSI_MPAM_NS | Meaning |
|---|---|
| 0b0 | PMCG MSIs that target a Secure PA use Secure |
| PARTID space. | |
| 0b1 | PMCG MSIs that target a Secure PA use |
| Non-secure PARTID space. |
This bit is RES0 if SMMU_PMCG_SCR.{NSMSI, NSRA} are configured for Non-secure MSIs.
See section 17.5 Assignment of PARTID and PMG for PMCG-originated MSIs .
The reset behavior of this field is:
- This field resets to ‘0’.
Otherwise:
Reserved, RES0.
NSMSI, bit [2]
When SMMUPMCGCFGR.MSI == 1:
Non-secure MSIs.
| NSMSI | Meaning |
|---|---|
| 0b0 | Generated MSIs target Secure PA space. |
| 0b1 | Generated MSIs target Non-secure PA space. |
The reset behavior of this field is:
- This field resets to ‘1’.
Otherwise:
Reserved, RES0.
NSRA, bit [1]
Non-secure register access.
| NSRA | Meaning |
|---|---|
| 0b0 | Non-secure Register Access is disabled. |
| • Non-secure access to any PMCG register is RAZ/WI. | |
| 0b1 | Non-secure Register Access is enabled. |
| • If the PMCG supports MSIs, generated MSIs target Non-secure | |
| PA space. |
The reset behavior of this field is:
- This field resets to ‘1’.
SO, bit [0]
Secure observation
| SO | Meaning |
|---|---|
| 0b0 | Secure observation is disabled. |
| • SMMU_PMCG_EVTYPERn.FILTER_SEC_SID is effectively 0. | |
| 0b1 | Secure observation is enabled. |
- See 10.6 Support for Secure state .
The reset behavior of this field is:
- This field resets to ‘0’.
Additional Information
If the PMCG does not implement support for Secure state, this register is RAZ/WI.
If the PMCG does not implement Secure state but the system does, both Secure and Non-secure accesses are permitted to PMCG registers. In this case, any MSIs generated from the PMCG must be issued to the Non-secure PA space.
Note: If software transitions control of a PMCG between Security states, Arm recommends following this procedure:
-
Set NSRA == 0 and NSMSI == 1.
-
Non-secure register access is disabled, but any active MSI configuration remains Non-secure.
-
Clear SMMU_PMCG_IRQ_CTRL.IRQEN and wait for Update of SMMU_PMCG_IRQ_CTRLACK.
-
Outstanding Non-secure MSIs are complete.
-
Set NSMSI == 0 and reprogram MSI registers as required.
Accessing SMMUPMCGSCR
If SMMU_PMCG_ROOTCR.ROOTCR_IMPL == 1, there is an alias of this register at offset 0xE40.
Accesses to this register use the following encodings:
Accessible at offset 0xDF8 from SMMUv3_PMCG
-
When an access is not Secure and an access is not Root, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
Accessible at offset 0xE40 from SMMUv3_PMCG
-
When an access is not Secure and an access is not Root, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.13 SMMU_PMCG_CFGR
The SMMU_PMCG_CFGR characteristics are:
Purpose
PMCG Configuration identification register.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CFGR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 | 31 26 25 24 23 22 21 20 19 14 13 8 7 6 5 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|
| RES0 | MSI | RES0 | SIZE | RES0 | NCTR | ||||||
| FILTER_PARTID_PMG MPAM | RELOC_CTRS CAPTURE SIDFILTERTYPE | ||||||||||
| __ |
Bits [31:26]
Reserved, RES0.
FILTERPARTIDPMG, bit [25]
This bit is Reserved, RES0 prior to SMMUv3.3.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| FILTER_PARTID_PMG | Meaning |
|---|---|
| 0b0 | This PMCG cannot flter |
| events by PARTID nor PMG. | |
| 0b1 | This PMCG can flter events |
| by PARTID and PMG. |
See section 10.4 StreamIDs and filtering .
Access to this field is RO.
MPAM, bit [24]
When SMMUPMCGCFGR.MSI == 1:
Memory Partitioning And Monitoring (MPAM) support.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| MPAM | Meaning |
|---|---|
| 0b0 | MPAM is not supported by the PMCG. |
| 0b1 | MPAM is supported by the PMCG. |
-
MPAM support is optional.
-
If the system supports MPAM but the PMCG does not, the PARTID and PMG values for PMCG-originated MSIs are zero.
-
This bit is Reserved, RES0 prior to SMMUv3.2.
-
Note: This field indicates that the PMCG supports issuing MSIs with PARTID and PMG information. Support for filtering of events by PARTID and PMG values is indicated in FILTER_PARTID_PMG.
Access to this field is RO.
Otherwise:
Reserved, RES0.
SIDFILTERTYPE, bit [23]
StreamID filter type.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| SID_FILTER_TYPE | Meaning |
|---|---|
| 0b0 | Separate StreamID or MPAM fltering is supported for each counter in |
| the PMCG. | |
| 0b1 | The StreamID or MPAM flter confgured bySMMU_PMCG_SMR0 |
| andSMMU_PMCG_EVTYPERn.{FILTER_SID_SPAN, | |
| FILTER_SEC_SID, FILTER_PARTID, FILTER_PMG, | |
| FILTER_MPAM_NS} applies to all counters in the PMCG. |
Access to this field is RO.
CAPTURE, bit [22]
Capture.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| CAPTURE | Meaning |
|---|---|
| 0b0 | Capture of counter values into SVRn registers not supported. |
| • SMMU_PMCG_SVRnandSMMU_PMCG_CAPRare RES0. | |
| 0b1 | Capture of counter values supported. |
Access to this field is RO.
MSI, bit [21]
Counter group supports Message Signalled Interrupt.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| MSI | Meaning |
|---|---|
| 0b0 | Group does not support MSI. |
| 0b1 | Group can send MSI. |
Access to this field is RO.
RELOCCTRS, bit [20]
Relocation controls.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| RELOC_CTRS | Meaning |
|---|---|
| 0b0 | Page 1 is not present, and the listed registers are |
| not relocated. | |
| 0b1 | Page 1 is present and the listed registers are |
| relocated to Page 1. |
-
When the value of this field is 1, the following registers are relocated to the equivalent offset on Page 1 (their Page 0 locations become RES0):
-
SMMU_PMCG_EVCNTRn.
-
SMMU_PMCG_SVRn.
-
SMMU_PMCG_OVSCLR0.
-
SMMU_PMCG_OVSSET0.
-
SMMU_PMCG_CAPR.
-
Access to this field is RO.
Bits [19:14]
Reserved, RES0.
SIZE, bits [13:8]
Size
- Size of PMCG counters in bits, minus one. Valid values are:
The value of this field is an IMPLEMENTATION DEFINED choice of:
| SIZE | Meaning |
|---|---|
| 0b011111 | 31 (32-bit counters). |
| 0b100011 | 35 (36-bit counters). |
| 0b100111 | 39 (40-bit counters). |
| 0b101011 | 43 (44-bit counters). |
| 0b101111 | 47 (48-bit counters). |
| 0b111111 | 63 (64-bit counters). |
All other values are reserved.
Access to this field is RO.
Bits [7:6]
Reserved, RES0.
NCTR, bits [5:0]
N counters.
This field has an IMPLEMENTATION DEFINED value.
- The number of counters available in the group is given by NCTR+1.
Access to this field is RO.
Additional Information
The capability of each counter group to send MSIs is specific to the group and is not affected by the core SMMU MSI capability (SMMU_IDR0.MSI).
Accessing SMMUPMCGCFGR
Accesses to this register use the following encodings:
Accessible at offset 0xE00 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.14 SMMU_PMCG_CR
The SMMU_PMCG_CR characteristics are:
Purpose
PMCG Control Register.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 1 0 | 31 1 0 |
|---|---|
| RES0 | E |
Bits [31:1]
Reserved, RES0.
E, bit [0]
Global counter enable.
- Global counter enable, where 1 == Enabled. When 0, no events are counted and values in SMMU_PMCG_EVCNTRn registers do not change. This bit takes precedence over the CNTEN bits set through SMMU_PMCG_CNTENSET0.
The reset behavior of this field is:
- This field resets to ‘0’.
Accessing SMMUPMCGCR
Accesses to this register use the following encodings:
Accessible at offset 0xE04 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RW.
10.5.2.15 SMMU_PMCG_IIDR
The SMMU_PMCG_IIDR characteristics are:
Purpose
SMMU PMCG Implementation Identification Register
Configuration
Implementation of this register is OPTIONAL.
Attributes
SMMU_PMCG_IIDR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 20 19 16 15 12 11 0 | 31 20 19 16 15 12 11 0 | 31 20 19 16 15 12 11 0 | 31 20 19 16 15 12 11 0 |
|---|---|---|---|
| ProductID | Variant | Revision | Implementer |
ProductID, bits [31:20]
This field has an IMPLEMENTATION DEFINED value.
Identifies the PMCG part.
Matches the {SMMU_PMCG_PIDR1.PART_1, SMMU_PMCG_PIDR0.PART_0} fields, if SMMU_PMCG_PIDR0 and SMMU_PMCG_PIDR1 are present.
Access to this field is RO.
Variant, bits [19:16]
This field has an IMPLEMENTATION DEFINED value.
Distinguishes product variants, or major revisions of the product.
Matches the SMMU_PMCG_PIDR2.REVISION field, if SMMU_PMCG_PIDR2 is present.
Access to this field is RO.
Revision, bits [15:12]
This field has an IMPLEMENTATION DEFINED value.
Distinguishes minor revisions of the product.
Matches the SMMU_PMCG_PIDR3.REVAND field, if SMMU_PMCG_PIDR3 is present.
Access to this field is RO.
Implementer, bits [11:0]
This field has an IMPLEMENTATION DEFINED value.
SMMU_PMCG_IIDR[11:8] contain the JEP106 continuation code for the implementer.
SMMU_PMCG_IIDR[7] is zero.
SMMU_PMCG_IIDR[6:0] contain the JEP106 identification code for the implementer.
SMMU_PMCG_IIDR[11:8] match SMMU_PMCG_PIDR4.DES_2 and SMMU_PMCG_IIDR[6:0] match the {SMMU_PMCG_PIDR2.DES_1, SMMU_PMCG_PIDR1.DES_0} fields, if SMMU_PMCG_PIDR{1, 2, 4} are present.
Access to this field is RO.
Additional Information
Note: Zero is not a valid JEP106 identification code. A value of zero for SMMU_PMCG_IIDR indicates this register is not implemented.
Note: For an Arm implementation, bits[11:0] are 0x43B.
Accessing SMMUPMCGIIDR
Accesses to this register use the following encodings:
Accessible at offset 0xE08 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.16 SMMU_PMCG_CEID0
The SMMU_PMCG_CEID0 characteristics are:
Purpose
Common Event ID bitmap, lower.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CEID0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| N | ||
| 31 | 0 | |
| N |
N, bits [63:0]
Event N.
Lower half of 128-bit bitmap comprised of two consecutive 64-bit registers.
In this register, bit (N & 63) relates to event number N, for 0 <= N < 64.
For each bit:
-
0b0: Event N cannot be counted by counters in this group.
-
0b1: Event N can be counted by counters in this group.
See section 10.3 Monitor events for event numbers.
Accessing SMMUPMCGCEID0
Accesses to this register use the following encodings:
Accessible at offset 0xE20 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.17 SMMU_PMCG_CEID1
The SMMU_PMCG_CEID1 characteristics are:
Purpose
Common Event ID bitmap, Upper.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_CEID1 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 63 | 32 | |
|---|---|---|
| N | ||
| 31 | 0 | |
| N |
N, bits [63:0]
Event N.
Upper half of 128-bit bitmap comprised of two consecutive 64-bit registers.
In this register, bit (N & 63) relates to event number N, for 64 <= N < 128.
For each bit
-
0b0: Event N cannot be counted by counters in this group.
-
0b1: Event N can be counted by counters in this group.
See section 10.3 Monitor events for event numbers.
Accessing SMMUPMCGCEID1
Accesses to this register use the following encodings:
Accessible at offset 0xE28 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.18 SMMU_PMCG_ROOTCR
The SMMU_PMCG_ROOTCR characteristics are:
Purpose
PMCG Root Control Register.
Configuration
This register is present only when SMMU_PMCG_ROOTCR.ROOTCR_IMPL == 1. Otherwise, direct accesses to SMMU_PMCG_ROOTCR are RES0.
Attributes
SMMU_PMCG_ROOTCR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 30 9 8 7 6 4 3 2 1 0
1 RES0 PMOSAO RES0 NAO RLORTO
ROOTCR_IMPL RES0
ROOTCRIMPL, bit [31]
Presence of SMMU_PMCG_ROOTCR
| ROOTCR_IMPL | Meaning |
|---|---|
| 0b1 | SMMU_PMCG_ROOTCR is implemented. |
Access to this field is RO.
Bits [30:9]
Reserved, RES0.
PMO, bit [8]
When SMMUROOTIDR0.GDI == 1:
Permit counting of events relating to Non-secure Protected Mode.
| PMO | Meaning |
|---|---|
| 0b0 | Counting of events relating to Non-secure Protected Mode is not permitted. |
| 0b1 | Counting of events relating to Non-secure Protected Mode is permitted. |
The reset behavior of this field is:
- This field resets to ‘0’.
Otherwise:
Reserved, RES0.
SAO, bit [7]
When SMMUROOTIDR0.GDI == 1:
Permit counting of events relating to System Agent state.
| SAO | Meaning |
|---|---|
| 0b0 | Counting of events relating to System Agent state is not permitted. |
| 0b1 | Counting of events relating to System Agent state is permitted. |
The reset behavior of this field is:
- This field resets to ‘0’.
Otherwise:
Reserved, RES0.
Bits [6:4]
Reserved, RES0.
NAO, bit [3]
Permit counting of events not attributable to a specific Security state.
| NAO | Meaning |
|---|---|
| 0b0 | Counting of non-attributable events is prevented. |
| 0b1 | Counting of non-attributable events is not prevented by this bit. |
Note: This bit has the opposite reset polarity to SMMU_PMCG_SCR.NAO. The ability to count non-attributable events is therefore controlled by Secure software by default. If this is unacceptable for the security model of a system, then Root firmware must clear this bit as part of system initialization. See also:
- 10.4.4 Counting of non-attributable events .
The reset behavior of this field is:
- This field resets to ‘1’.
Bit [2]
Reserved, RES0.
RLO, bit [1]
Permit counting of events relating to Realm StreamIDs.
| RLO | Meaning |
|---|---|
| 0b0 | Counting of events relating to Realm StreamIDs is not permitted. |
| 0b1 | Counting of events relating to Realm StreamIDs is permitted. |
See also:
- SMMU_PMCG_EVTYPERn.FILTER_REALM_SID.
The reset behavior of this field is:
- This field resets to ‘0’.
RTO, bit [0]
Permit counting of events relating to Root state.
| RTO | Meaning |
|---|---|
| 0b0 | Counting of events relating to Root state is not permitted. |
| 0b1 | Counting of events relating to Root state is permitted. |
The reset behavior of this field is:
- This field resets to ‘0’.
Accessing SMMUPMCGROOTCR
Accesses to this register use the following encodings:
Accessible at offset 0xE48 from SMMUv3_PMCG
-
When an access is Root, accesses to this register are RW.
-
Otherwise, accesses to this register are RO.
10.5.2.19 SMMU_PMCG_IRQ_CTRL
The SMMU_PMCG_IRQ_CTRL characteristics are:
Purpose
PMCG IRQ enable and control register.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_IRQ_CTRL is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 1 0
RES0
IRQEN
Bits [31:1]
Reserved, RES0.
IRQEN, bit [0]
IRQ enable
The reset behavior of this field is:
- This field resets to ‘0’.
Additional Information
Each field in this register has a corresponding field in SMMU_PMCG_IRQ_CTRLACK, with the same Update semantic as fields in SMMU_CR0 versus SMMU_CR0ACK.
This register contains the main IRQ enable flag for a per-counter group interrupt source. This enable allows or inhibits both edge-triggered wired outputs (if implemented) and MSI writes (if supported by the counter group). When IRQEN == 0, no interrupt is triggered regardless of individual per-counter overflow INTEN flags (that is, they are overridden). IRQEN also controls overall interrupt completion and MSI configuration changes.
When MSIs are supported, as indicated by SMMU_PMCG_CFGR.MSI == 1, IRQ enable flags Guard the MSI address and data payload registers, which must only be changed when their respective enable flag is 0. See SMMU_PMCG_IRQ_CFG0 for details.
Completion of Update to IRQ enables guarantees the following side effects:
-
Completion of an Update of IRQEN from 0 to 1 guarantees that the MSI configuration in SMMU_PMCG_IRQ_CFG{0,1,2} will be used for all future MSIs generated from the counter group.
-
An Update of IRQEN from 1 to 0 completes when all prior MSIs have become visible to their Shareability domain (have completed). Completion of this Update guarantees that no new MSI writes or wired edge events will later become visible from this source.
An IRQ is triggered from the PMCG if all of the following occur:
-
SMMU_PMCG_IRQ_CTRL.IRQEN == 1.
-
A counter overflows and sets an OVS bit, whose corresponding INTEN bit was set through SMMU_PMCG_INTENSET0.
Accessing SMMUPMCGIRQCTRL
Accesses to this register use the following encodings:
Accessible at offset 0xE50 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
• Otherwise, accesses to this register are RW.
10.5.2.20 SMMU_PMCG_IRQ_CTRLACK
The SMMU_PMCG_IRQ_CTRLACK characteristics are:
Purpose
Provides acknowledgment of changes to PMCG IRQ enable and control register, SMMU_PMCG_IRQ_CTRL.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_IRQ_CTRLACK is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 1 0
RES0
IRQEN
Bits [31:1]
Reserved, RES0.
IRQEN, bit [0]
IRQ enable.
Acknowledge bit for SMMU_PMCG_IRQ_CTRL.IRQEN.
The reset behavior of this field is:
- This field resets to ‘0’.
Additional Information
Undefined bits read as zero. Fields in this register are RES0 if their corresponding SMMU_PMCG_IRQ_CTRL field is Reserved.
Accessing SMMUPMCGIRQCTRLACK
Accesses to this register use the following encodings:
Accessible at offset 0xE54 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.21 SMMU_PMCG_IRQ_CFG0
The SMMU_PMCG_IRQ_CFG0 characteristics are:
Purpose
PMCG MSI configuration register.
Configuration
This register is present only when SMMU_PMCG_CFGR.MSI == 1. Otherwise, direct accesses to SMMU_PMCG_IRQ_CFG0 are RES0.
Attributes
SMMU_PMCG_IRQ_CFG0 is a 64-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
63 56 55 32
RES0 ADDR[55:2]
31 2 1 0
ADDR[55:2] RES0
Bits [63:56]
Reserved, RES0.
ADDR, bits [55:2]
Physical address of MSI target, bits [55:2].
- High-order bits of the ADDR field above the system physical address size, as reported by SMMU_IDR5.OAS, are RES0.
Note: An implementation is not required to store these bits.
- Bits [1:0] of the effective address that results from this field are zero.
If ADDR == 0, no MSI is sent. This allows a wired IRQ, if implemented, to be used instead of an MSI. The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Bits [1:0]
Reserved, RES0.
Additional Information
When an implementation does not support MSIs, all fields are RES0.
See SMMU_PMCG_SCR.NSMSI for control of the target PA space of the MSI.
Accessing SMMUPMCGIRQCFG0
SMMU_PMCG_IRQ_CFG0 is Guarded by SMMU_PMCG_IRQ_CTRL.IRQEN and must only be modified when IRQEN == 0. SMMU_PMCG_IRQ_CFG{0,1,2} have the same behaviors as SMMU_*_IRQ_CFG{0,1,2} with respect to their enables, including the permitted behaviors of writes when IRQEN == 1.
Accesses to this register use the following encodings:
Accessible at offset 0xE58 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
• When SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRL.IRQEN == ‘1’ or SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRLACK.IRQEN == ‘1’, accesses to this register are RO.
-
Otherwise, accesses to this register are RW.
10.5.2.22 SMMU_PMCG_IRQ_CFG1
The SMMU_PMCG_IRQ_CFG1 characteristics are:
Purpose
PMCG MSI configuration register.
Configuration
This register is present only when SMMU_PMCG_CFGR.MSI == 1. Otherwise, direct accesses to SMMU_PMCG_IRQ_CFG1 are RES0.
Attributes
SMMU_PMCG_IRQ_CFG1 is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 | 0 | |
|---|---|---|
| DATA |
When an implementation does not support MSIs, all fields are RES0.
DATA, bits [31:0]
MSI data payload.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Accessing SMMUPMCGIRQCFG1
SMMU_PMCG_IRQ_CFG1 is Guarded by SMMU_PMCG_IRQ_CTRL.IRQEN and must only be modified when IRQEN == 0.
Accesses to this register use the following encodings:
Accessible at offset 0xE60 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
• When SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRL.IRQEN == ‘1’ or SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRLACK.IRQEN == ‘1’, accesses to this register are RO.
-
Otherwise, accesses to this register are RW.
10.5.2.23 SMMU_PMCG_IRQ_CFG2
The SMMU_PMCG_IRQ_CFG2 characteristics are:
Purpose
PMCG MSI configuration register.
Configuration
This register is present only when SMMU_PMCG_CFGR.MSI == 1. Otherwise, direct accesses to SMMU_PMCG_IRQ_CFG2 are RES0.
Attributes
SMMU_PMCG_IRQ_CFG2 is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 6 5 4 3 0
RES0 SH MEMATTR
Bits [31:6]
Reserved, RES0.
SH, bits [5:4]
Shareability.
| SH | Meaning |
|---|---|
| 0b00 | Non-shareable. |
| 0b01 | Reserved, behaves as 0b00. |
| 0b10 | Outer Shareable. |
| 0b11 | Inner Shareable. |
- When MemAttr encodes a Device memory type, the value of this field is IGNORED and the Shareability is effectively Outer Shareable.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
MEMATTR, bits [3:0]
Memory type.
- Encoded the same as the STE.MemAttr field.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Additional Information
When an implementation does not support MSIs, all fields are RES0.
Accessing SMMUPMCGIRQCFG2
SMMU_PMCG_IRQ_CFG2 is Guarded by SMMU_PMCG_IRQ_CTRL.IRQEN and must only be modified when IRQEN == 0.
Accesses to this register use the following encodings:
Accessible at offset 0xE64 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
• When SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRL.IRQEN == ‘1’ or SMMUv3_PMCG.SMMU_PMCG_IRQ_CTRLACK.IRQEN == ‘1’, accesses to this register are RO.
-
Otherwise, accesses to this register are RW.
10.5.2.24 SMMU_PMCG_IRQ_STATUS
The SMMU_PMCG_IRQ_STATUS characteristics are:
Purpose
PMCG MSI Status register.
Configuration
This register is present only when SMMU_PMCG_CFGR.MSI == 1. Otherwise, direct accesses to SMMU_PMCG_IRQ_STATUS are RES0.
Attributes
SMMU_PMCG_IRQ_STATUS is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 1 0
RES0
IRQ_ABT
Bits [31:1]
Reserved, RES0.
IRQABT, bit [0]
MSI abort.
-
The SMMU sets this bit to 1 if it detects that an MSI has terminated with an abort.
-
This bit is RES0 when SMMU_PMCG_CFGR.MSI == 0.
-
It is IMPLEMENTATION DEFINED whether an implementation can detect this condition.
-
This bit is cleared to 0 when SMMU_PMCG_IRQ_CTRL.IRQEN is Updated from 0 to 1.
- Note: An IRQEN transition from 1 to 0 does not clear this bit, as this transition also ensures visibility of outstanding MSI writes and clearing IRQ_ABT at this point might mask possible abort completions of those MSI writes.
The reset behavior of this field is:
- This field resets to an UNKNOWN value.
Accessing SMMUPMCGIRQSTATUS
In SMMUv3.0, this register location is RES0.
Accesses to this register use the following encodings:
Accessible at offset 0xE68 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.25 SMMU_PMCG_GMPAM
The SMMU_PMCG_GMPAM characteristics are:
Purpose
MPAM configuration for PMCG-originated MSI transactions.
Configuration
This register is present only when SMMU_PMCG_CFGR.MPAM == 1. Otherwise, direct accesses to SMMU_PMCG_GMPAM are RES0.
Attributes
SMMU_PMCG_GMPAM is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 30 24 23 16 15 0 | 31 30 24 23 16 15 0 | 31 30 24 23 16 15 0 | 31 30 24 23 16 15 0 | 31 30 24 23 16 15 0 |
|---|---|---|---|---|
| RES0 | PO_PMG | PO_PARTID | ||
| Update |
The configuration of SMMU_PMCG_SCR.NSMSI and SMMU_PMCG_SCR.NSRA affects whether this register configures Non-secure or Secure PARTID and PMG values, and therefore the maximum supported values for PARTID and PMG.
See section 17.5 Assignment of PARTID and PMG for PMCG-originated MSIs for details.
Update, bit [31]
Update completion flag.
The reset behavior of this field is:
- This field resets to ‘0’.
Bits [30:24]
Reserved, RES0.
POPMG, bits [23:16]
PMG of PMCG-orientated MSI transactions.
-
This field determines the PMG of PMCG-originated MSI transactions.
-
Bits above the combined PMG bit width, as indicated by the greater of SMMU_PMCG_MPAMIDR.PMG_MAX and SMMU_PMCG_S_MPAMIDR.PMG_MAX, are RES0.
-
If a value is programmed that is greater than the corresponding PMG_MAX limit, an UNKNOWN PMG is used.
The reset behavior of this field is:
- This field resets to 0x00.
POPARTID, bits [15:0]
PARTID of PMCG-originated MSI transactions
-
This field determines the PARTID of PMCG-originated MSI transactions.
-
Bits above the combined PARTID bit width, as indicated by the greater of SMMU_PMCG_MPAMIDR.PARTID_MAX and SMMU_PMCG_S_MPAMIDR.PARTID_MAX, are RES0.
-
If a value is programmed that is greater than the corresponding PARTID_MAX limit, an UNKNOWN PARTID is used.
The reset behavior of this field is:
- This field resets to 0x0000.
Additional Information
The PO_PMG and PO_PARTID values determine the MPAM attributes applied to PMCG MSI write transactions.
The Update flag is similar to the SMMU_(*_)GMPAM.Update mechanism. It indicates that a change to the register has been accepted and when the Update flag is observed to be zero after a correct update procedure, the new values are guaranteed to be applied to future PMCG-originated accesses.
This register must only be written when Update == 0. A write when an Update == 1, that is when a prior update is underway, is CONSTRAINED UNPREDICTABLE and has one of the following behaviors:
-
Update completes with any value.
-
Note: The effective IDs in use might not match those read back from this register.
-
The write is ignored and update completes using the initial value.
If this register is written without simultaneously setting Update to 1, the effect is CONSTRAINED UNPREDICTABLE and has one of the following behaviors:
-
The write is ignored.
-
The written value is stored and is visible to future reads of the register, but does not affect transactions.
-
The written value affects transactions at an UNPREDICTABLE update point:
-
There is no guarantee that all future PMCG-originated accesses after the write will take the new value.
When a write to this register correctly follows the requirements in this section, the new value is observable to future reads of the register even if they occur before the Update has completed.
Note: The Update mechanism provides a way to guarantee that future MSI accesses will use the configured MPAM IDs. It does not synchronize prior or ongoing accesses, which must be completed using existing facilities. For example, prior MSI writes can be completed by updating the corresponding IRQEN to a disabled state.
Note: If a change is made to the Non-secure Register Access, SMMU_PMCG_SCR.NSRA, or MSI target PA space configuration, SMMU_PMCG_SCR.NSMSI, then the configuration in this register might be invalid in the new configuration.
Note: For example, a Secure PARTID value might not be valid if it is later treated as a Non-secure PARTID value. Or, the existing value might be greater than the corresponding PARTID_MAX in the new configuration and will be treated as an UNKNOWN value.
Note: When the Security state of the MSI changes, this configuration should be Updated to the required value. Because this scenario might occur when ownership of the MSI configuration changes, a new owner must consider that a previous Update initiated by the previous owner might still be ongoing and must check that this Update has completed before performing a new Update.
Accessing SMMUPMCGGMPAM
Accesses to this register use the following encodings:
Accessible at offset 0xE6C from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
When SMMUv3_PMCG.SMMU_PMCG_GMPAM.Update == ‘1’, accesses to this register are RO.
-
Otherwise, accesses to this register are RW.
10.5.2.26 SMMU_PMCG_AIDR
The SMMU_PMCG_AIDR characteristics are:
Purpose
This register identifies the SMMU architecture version to which the PMCG implementation conforms.
Configuration
There are no configuration notes.
Attributes
SMMU_PMCG_AIDR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
| 31 8 7 4 3 0 | 31 8 7 4 3 0 | 31 8 7 4 3 0 | 31 8 7 4 3 0 |
|---|---|---|---|
| RES0 | 0 0 0 0 | ArchMinorRev | |
| ArchMajorRev |
Bits [31:8]
Reserved, RES0.
ArchMajorRev, bits [7:4]
| ArchMajorRev | Meaning |
|---|---|
| 0b0000 | SMMUv3.x. |
Access to this field is RO.
ArchMinorRev, bits [3:0]
The value of this field is an IMPLEMENTATION DEFINED choice of:
| ArchMinorRev | Meaning |
|---|---|
| 0b0000 | SMMUv3.0. |
| 0b0001 | SMMUv3.1. |
| 0b0010 | SMMUv3.2. |
| 0b0011 | SMMUv3.3. |
| 0b0100 | SMMUv3.4. |
| 0b0101 | SMMUv3.5. |
Access to this field is RO.
Additional Information
When considered as {ArchMajorRev, ArchMinorRev}:
-
[7:0] == 0x00 == SMMUv3.0 PMCG.
-
[7:0] == 0x01 == SMMUv3.1 PMCG.
-
[7:0] == 0x02 == SMMUv3.2 PMCG.
-
[7:0] == 0x03 == SMMUv3.3 PMCG.
-
[7:0] == 0x04 == SMMUv3.4 PMCG.
-
[7:0] == 0x05 == SMMUv3.5 PMCG.
-
All other values Reserved.
Accessing SMMUPMCGAIDR
Accesses to this register use the following encodings:
Accessible at offset 0xE70 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
• Otherwise, accesses to this register are RO.
10.5.2.27 SMMU_PMCG_MPAMIDR
The SMMU_PMCG_MPAMIDR characteristics are:
Purpose
Per-PMCG Non-secure MPAM capability identification when the PMCG supports MSIs.
Configuration
This register is present only when SMMU_PMCG_CFGR.MPAM == 1 or SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1. Otherwise, direct accesses to SMMU_PMCG_MPAMIDR are RES0.
Attributes
SMMU_PMCG_MPAMIDR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 24 23 16 15 0
RES0 PMG_MAX PARTID_MAX
Bits [31:24]
Reserved, RES0.
PMGMAX, bits [23:16]
Maximum Non-secure PMG value.
This field has an IMPLEMENTATION DEFINED value.
-
The maximum Non-secure PMG value that is permitted to be used by this PMCG for Non-secure MSIs. This field is RES0 when MPAM is not supported, as indicated by SMMU_PMCG_CFGR.MPAM == 0.
-
Access to this field is RO.
PARTIDMAX, bits [15:0]
Maximum Non-secure PARTID value.
This field has an IMPLEMENTATION DEFINED value.
- The maximum Non-secure PARTID value that is permitted to be used by this PMCG for Non-secure MSIs. This field is RES0 when MPAM is not supported, as indicated by SMMU_PMCG_CFGR.MPAM == 0.
Access to this field is RO.
Additional Information
The PMCG Non-secure PMG bit width is defined as the bit position of the most-significant 1 in PMG_MAX[7:0], plus one, or is defined as zero if PMG_MAX is zero.
Note: For example, if PMG_MAX == 0x0f, the PMG bit width is 4.
The PMCG Non-secure PARTID bit width is defined as the bit position of the most-significant 1 in PARTID_MAX[15:0], plus one, or is defined as zero if PARTID_MAX is zero.
Note: For example, if PARTID_MAX == 0x0034, the PARTID bit width is 6.
Note: PMG_MAX and PARTID_MAX specify the maximum values of each ID type that can be configured in the PMCG for a Non-secure MSI. These values do not describe properties of the rest of the system, which are discovered using mechanisms that are outside the scope of this specification.
Note: PMG_MAX is architecturally permitted to be zero-sized when MPAM is supported by the PMCG.
Note: Because a PMCG might be implemented in a component related to, but separate from the main SMMU, the MPAM capabilities of each PMCG are independent from the MPAM capabilities of the main SMMU.
Accessing SMMUPMCGMPAMIDR
Accesses to this register use the following encodings:
Accessible at offset 0xE74 from SMMUv3_PMCG
-
When an access is Non-secure, the PMCG supports Secure state, and SMMUv3_PMCG.SMMU_PMCG_SCR.NSRA == ‘0’, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.28 SMMU_PMCG_S_MPAMIDR
The SMMU_PMCG_S_MPAMIDR characteristics are:
Purpose
Per-PMCG Secure MPAM capability identification when the PMCG supports MSIs.
Configuration
This register is present only when the PMCG supports Secure state and (SMMU_PMCG_CFGR.MPAM == 1 or SMMU_PMCG_CFGR.FILTER_PARTID_PMG == 1). Otherwise, direct accesses to SMMU_PMCG_S_MPAMIDR are RES0.
Attributes
SMMU_PMCG_S_MPAMIDR is a 32-bit register.
This register is part of the SMMUv3_PMCG block.
Field descriptions
31 26 25 24 23 16 15 0
RES0 PMG_MAX PARTID_MAX
HAS_MPAM_NS RES0
Bits [31:26]
Reserved, RES0.
HASMPAMNS, bit [25]
See SMMU_PMCG_SCR.MSI_MPAM_NS.
The value of this field is an IMPLEMENTATION DEFINED choice of:
| HAS_MPAM_NS | Meaning |
|---|---|
| 0b0 | The MPAM_NS mechanism for Secure state is not |
| implemented. | |
| 0b1 | The MPAM_NS mechanism for Secure state is |
| implemented. |
If SMMU_PMCG_CFGR.MSI == 0, HAS_MPAM_NS is RES0.
Access to this field is RO.
Bit [24]
Reserved, RES0.
PMGMAX, bits [23:16]
Maximum Secure PMG value.
This field has an IMPLEMENTATION DEFINED value.
- The maximum Secure PMG value that is permitted to be used by this PMCG for Secure MSIs. This field is RES0 when MPAM is not supported, as indicated by SMMU_PMCG_CFGR.MPAM == 0.
Access to this field is RO.
PARTIDMAX, bits [15:0]
Maximum Secure PARTID value.
This field has an IMPLEMENTATION DEFINED value.
- The maximum Secure PARTID value that is permitted to be used by this PMCG for Secure MSIs. This field is RES0 when MPAM is not supported, as indicated by SMMU_PMCG_CFGR.MPAM == 0.
Access to this field is RO.
Additional Information
This register is similar to SMMU_PMCG_MPAMIDR except describes the Secure MPAM facilities of the PMCG.
The PMCG Secure PMG bit width is defined as the bit position of the most-significant 1 in PMG_MAX[7:0], plus one, or is defined as zero if PMG_MAX is zero.
The PMCG Secure PARTID bit width is defined as the bit position of the most-significant 1 in PARTID_MAX[15:0], plus one, or is defined as zero if PARTID_MAX is zero.
Accessing SMMUPMCGSMPAMIDR
Accesses to this register use the following encodings:
Accessible at offset 0xE78 from SMMUv3_PMCG
-
When an access is not Secure and an access is not Root, accesses to this register are RAZ/WI.
-
Otherwise, accesses to this register are RO.
10.5.2.29 SMMU_PMCG_ID_REGS
SMMU_PMCG register offsets 0xFB0-0xFFC are defined as a read-only identification register space. For Arm implementations of the SMMU architecture the assignment of this register space, and naming of registers in this space, is consistent with the Arm identification scheme for CoreLink and CoreSight components. Arm strongly recommends that other implementers also use this scheme to provide a consistent software discovery model.
For Arm implementations, the following assignment of fields, consistent with CoreSight ID registers [10], is used:
| Offset Name (SMMU_PMCG_- Prefxed) | Field Value Meaning |
|---|---|
| 0xFF0 CIDR0, Component ID0 | [7:0] 0x0D Preamble |
| 0xFF4 CIDR1, Component ID1 | [7:4] 0x9 CLASS |
| [3:0] 0x0 Preamble | |
| 0xFF8 CIDR2, Component ID2 | [7:0] 0x05 Preamble |
| 0xFFC CIDR3, Component ID3 | [7:0] 0xB1 Preamble |
| 0xFE0 PIDR0, Peripheral ID0 | [7:0] IMP DEF Part_0: bits [7:0] of the Part number |
| 0xFE4 PIDR1, Peripheral ID1 | [7:4] IMP DEF DES_0: bits [3:0] of the JEP106 Designer code |
| Offset Name (SMMU_PMCG_- Prefxed) | Field Value Meaning |
|---|---|
| [3:0] IMP DEF PART_1: bits [11:8] of the Part number | |
| 0xFE8 PIDR2, Peripheral ID2 | [7:4] IMP DEF REVISION |
| [3] 1 JEDEC-assigned value for DES always used | |
| [2:0] IMP DEF DES_1: bits [6:4] bits of the JEP106 Designer code | |
| 0xFEC PIDR3, Peripheral ID3 | [7:4] IMP DEF REVAND |
| [3:0] IMP DEF CMOD | |
| 0xFD0 PIDR4, Peripheral ID4 | [7:4] 0 SIZE |
| [3:0] IMP DEF DES_2: JEP106 Designer continuation code | |
| 0xFD4 PIDR5, Peripheral ID5 | RES0 Reserved |
| 0xFD8 PIDR6, Peripheral ID6 | RES0 Reserved |
| 0xFDC PIDR7, Peripheral ID7 | RES0 Reserved |
| 0xFBC PMDEVARCH | [31:21] 0x23B ARCHITECT (0x23Bis the resulting encoding of Arm’s JEP106 code) |
| [20] 1 PRESENT | |
| [19:16] 0 REVISION | |
| [15:0] 0x2A56 ARCHID | |
| 0xFCC PMDEVTYPE | [7:4] 5 Sub-type: Associated with an SMMU |
| [3:0] 6 Class: Performance monitor device type |
Fields outside of those defined in this table are RES0.
Note: The Designer code fields (DES_*) fields for Arm-designed implementations use continuation code 0x4 and Designer code 0x3B.
Note: Non-Arm implementations that follow this CoreSight ID register layout must set the Designer fields appropriate to the implementer.
10.6 Support for Secure state
Support for Secure state in a PMCG is optional. If supported, it comprises of:
-
Whether the PMCG registers can be accessed by both Non-secure and Secure accesses, or only Secure accesses.
-
Whether the counters can observe events associated with Secure StreamIDs or Secure state.
-
Whether an MSI targets the Secure or Non-secure PA space.
The SMMU_PMCG_SCR.NSRA flag controls whether Non-secure accesses can be made to the registers of a given group. Secure accesses can always be made to the registers.
Note: As counter groups might exist in separate components, the SMMU does not contain a centralized mechanism for assigning counter groups to a Security state.
The SMMU_PMCG_SCR.SO flag controls whether counters can observe events associated with Secure state or Secure StreamIDs.
When SMMU_PMCG_SCR.SO == 1, Secure observation is enabled and:
-
Counters using event types that can be filtered by StreamID might count events that are associated with a Secure or Non-secure StreamID. See section 10.4 StreamIDs and filtering and the SMMU_PMCG_EVTYPERn .FILTER_SEC_SID bit.
-
Counters using other event types are able to count events that are associated with Secure or Non-secure state, as appropriate for the event.
Note: IMPLEMENTATION DEFINED events might be associated with StreamIDs or a Security state even if they might not be directly associated with a specific StreamID. The architected global events are not specific to a Security state.
When SMMU_PMCG_SCR.SO == 0, Secure observation is disabled and:
-
Counters using event types that can be filtered by StreamID only count events associated with Non-secure StreamIDs.
-
Counters using other event types only count events that are associated with the Non-secure state.
When a counter uses an event type able to be filtered by StreamID but the StreamID filter matches all, events from all StreamIDs associated with the Security state selected by the SMMU_PMCG_EVTYPERn.FILTER_SECSID bit are counted, if permitted by the ‘SO’ flag.
If a counter group supports MSIs:
-
If Secure state is not supported in the PMCG, the target PA space of the MSI is Non-secure.
-
If Secure state is supported in the PMCG, the target PA space of the MSI is given by:
NS = SMMU_PMCG_SCR.NSMSI | SMMU_PMCG_SCR.NSRA
See section SMMU_PMCG_SCR.
If a PMCG does not support Secure state but the system does, then the PMCG only observes events that are associated with Non-secure streams. If a PMCG supports Secure state but the system does not, then all streams are considered to be Non-secure.
10.7 Support for Realm state
The presence of SMMU PMCG controls for Realm and Root states is indicated in SMMU_PMCG_ROOTCR.ROOTCR_IMPL.
Arm strongly recommends that if an SMMU has SMMU_ROOT_IDR0.REALM_IMPL = 1, then any SMMU PMCGs associated with that SMMU have SMMU_PMCG_ROOTCR.ROOTCR_IMPL = 1.